How to Create Volatile Registry Keys: New Utility!
Written by Jacques Bensimon
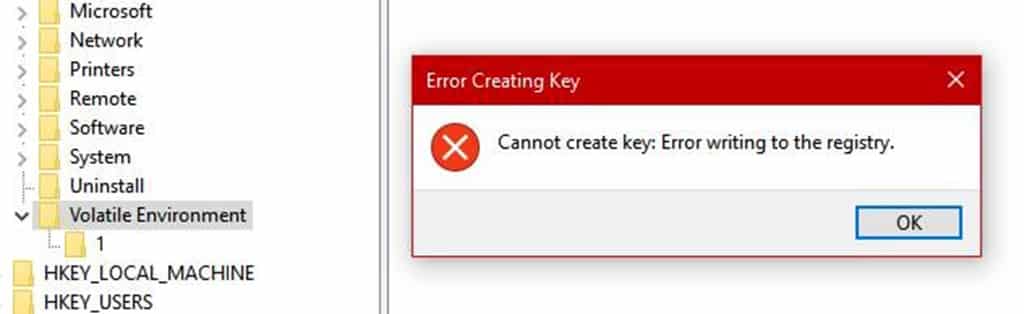
While working on an upcoming post and the new utility it will introduce, I had the need to create volatile Registry keys. If you’re not familiar with them, volatile keys explode when disturbed … just kidding, they’re keys that only exist in memory and are never stored in their corresponding hive file, i.e. they disappear as soon as their hive is unloaded, typically at logoff in the case of user keys and at shutdown or restart in the case of machine keys. Windows uses them in several places, often to store session-specific data that won’t necessarily apply to future sessions and therefore are best not made persistent. Problem was, neither Regedit.exe nor Reg.exe (nor as far as I can figure out PowerShell) can create volatile keys, not even subkeys of existing volatile keys. For example, as shown in this screenshot, trying to create a subkey of the well-known volatile key “HKCU\Volatile Environment”, where session-specific environment variables are stored, using Regedit fails (with a not particularly informative error message) because volatile keys cannot have non-volatile subkeys, the only kind Regedit can create.
I therefore whipped up the quick little command line utility VolatileKey to create volatile keys.
You can get the latest version of the utility directly from my github repo here:
https://github.com/CCOSTAN/BlogPostStorage
It offers no syntax help, so all the necessary usage information follows:
Syntax: VolatileKey.exe RootKey Subkey_Path, where RootKey must be one of HKCU, HKLM or HKU (or of their full names HKEY_CURRENT_USER, etc.), case-insensitive.
Example: VolatileKey HKCU "Software\VolKey\Vol Subkey"
- When the utility creates multiple new subkeys in one go, as in the example, they’ll all be volatile, so if you need some initial portion of the subkey path to consist of “normal” (non-volatile) keys, pre-create that part of the subkey path using Reg.exe or other tools before invoking VolatileKey.exe.
- Once a volatile key is created, you can use normal tools (Regedit, Reg, PowerShell, etc.) to populate it with values.
- The utility uses return code (ErrorLevel) 0 to report success, 99 for incorrect syntax (fewer or more than exactly two arguments, or a first argument that doesn’t match one of the six allowed root key names), and a standard Windows error code otherwise (which can be interpreted by running NET HELPMSG #), for example 5 = Access Denied.
- Note that subkeys (volatile or otherwise) cannot be created directly under HKLM and HKU – one of their hive subkeys must be specified, for example HKLM\Software\… or HKU\{user_SID}\…
- Finally, the utility is compiled 32-bits, but can access the full 64-bit Registry view on x64 platforms, so no 64-bit version is provided or necessary.
Carlo, our intrepid blogmaster, insists on use cases being presented when introducing a new utility, and I admit he had me stumped on this one, but here’s what comes to mind: a volatile key can be used as a “scratchpad” of sorts for scripts to keep track of their activities in the course of a session, to quietly return results, or to pass information to cooperating scripts. The beauty of a volatile key for these purposes is that it’s guaranteed to be gone in a future session, plus using one for scratchpad info is faster, more convenient, and more elegant than writing to a temporary file (that you may then have to delete at some point). Bottom line, though, I think this utility simply plugs a hole in the scripter’s toolkit — whatever the purpose, it should be possible to easily create volatile keys without having to resort to API calls, and I was surprised not to find a tool that does it, … and we now have one.
That’s it for now. Stay tuned to this space for the next utility: I’m pretty sure you’ll like it.
JB
To stay up on Citrix and Microsoft ramblings among other things, be sure to follow Jacques on twitter: @JacqBens.